[ GUIDE / WALLETS ]
Anatomy of a Wallet
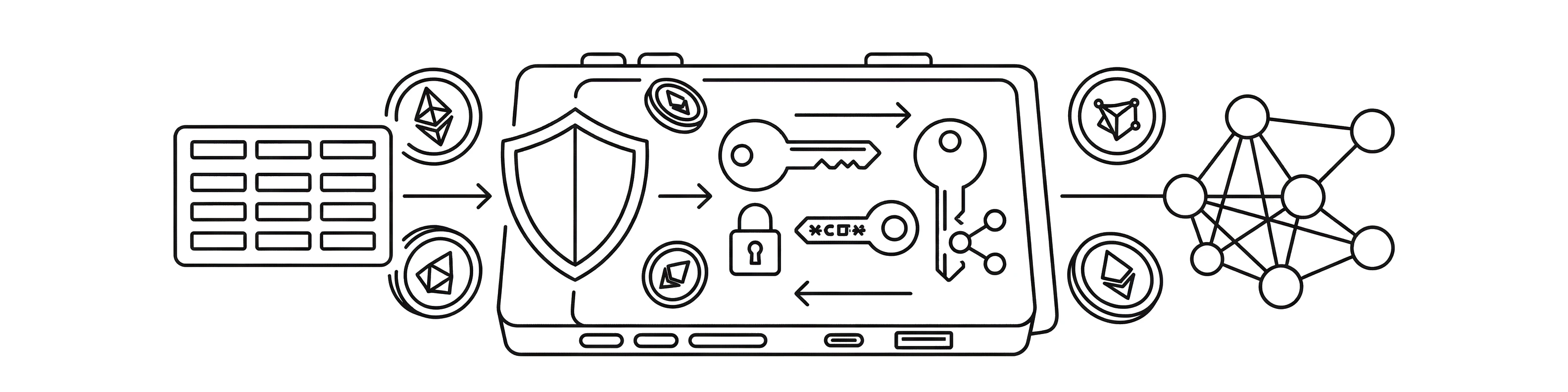
How cryptocurrency wallets work under the hood — from key derivation and address generation to transaction signing and broadcast.
What is a crypto wallet and how does it work?
What Is a Crypto Wallet?
A cryptocurrency wallet is a tool that stores your private keys and allows you to send, receive, and manage digital assets. Despite the name, wallets don't actually store your coins or tokens — those exist as records on the blockchain. Your wallet holds the cryptographic keys that prove your ownership and authorize transfers.
A wallet is more like a keychain than a wallet. It doesn't hold money — it holds the keys that unlock your money on the blockchain.
Wallets come in many forms, each designed for different use cases:
- Mobile apps — convenient, always with you, ideal for everyday transactions
- Desktop software — more control, larger screen, suitable for managing multiple accounts
- Browser extensions — seamless interaction with DeFi protocols and dApps
- Hardware devices — maximum security, keys are generated and stored on a dedicated chip that never connects to the internet
- Paper wallets — a printed private key or seed phrase for long-term cold storage (now largely deprecated in favor of hardware wallets)
Regardless of the form, every wallet performs the same core functions: key storage, address generation, transaction creation, and signature production.
What is the difference between a public key and a private key?
Public Keys vs. Private Keys
Every wallet is built on asymmetric cryptography — a system that uses two mathematically related but functionally different keys:
- Private key — a secret 256-bit number that authorizes spending. This must never be shared with anyone. Whoever controls the private key controls the funds.
- Public key — derived mathematically from the private key using elliptic curve multiplication. It can be freely shared and is used to verify signatures and generate addresses.
The private key is like a signature stamp — it proves you are the owner and authorizes actions. The public key is like your mailing address — anyone can send things to it, but only you can access the contents.
The mathematical relationship between the two keys is one-directional: you can always derive the public key from the private key, but it is computationally infeasible to derive the private key from the public key. This asymmetry is the foundation of all cryptocurrency security.
How are cryptocurrency addresses generated?
Addresses and Receiving Funds
An address is derived from your public key through a series of hashing and encoding steps. It is the string you share with others to receive funds — like a bank account number, but pseudonymous and verifiable by anyone on the network.
Address Formats in Bitcoin
- Legacy (P2PKH) — starts with
1, the original format - Nested SegWit (P2SH) — starts with
3, backward-compatible SegWit - Native SegWit (Bech32) — starts with
bc1q, lower fees, better error detection - Taproot (Bech32m) — starts with
bc1p, latest format with enhanced privacy and scripting capabilities
For Ethereum and EVM chains, addresses are 40-character hex strings prefixed with 0x, derived from the last 20 bytes of the Keccak-256 hash of the public key.
How does transaction signing work in crypto?
Sending Funds — Transaction Signing
When you send cryptocurrency, your wallet performs a precise sequence of steps:
- Construct the transaction — specify the recipient address, amount, and fee
- Create a hash — the wallet computes a cryptographic hash of the transaction data
- Sign the hash — your private key produces a digital signature over the hash
- Broadcast — the signed transaction is sent to the network
- Verification — network nodes verify the signature against your public key to confirm authorization
The beauty of this system is that the private key is used to create the signature, but the public key is sufficient to verify it. Your private key never leaves the wallet during a transaction — only the signature does.
Signing a transaction is like signing a check with invisible ink that only reveals itself under a specific UV light (your public key). Anyone can verify it is genuine, but no one can forge your signature.
What is an HD wallet and why does it use one seed for many keys?
HD Wallets — One Seed, Unlimited Keys
Modern wallets are Hierarchical Deterministic (HD), meaning they derive all private keys, public keys, and addresses from a single seed phrase using a tree-like structure.
This design provides powerful advantages:
- Single backup — one seed phrase protects all current and future keys
- Multi-coin support — the same seed can derive keys for Bitcoin, Ethereum, and dozens of other cryptocurrencies simultaneously
- Automatic address generation — wallets generate fresh receiving addresses without user intervention
- Account isolation — different derivation paths create logically separate accounts under one seed
How does BIP32 hierarchical deterministic derivation work?
BIP32 Hierarchical Deterministic Derivation
BIP32 defines a tree structure for key derivation. Starting from a master key (derived from the BIP39 seed via HMAC-SHA512), child keys are generated at each level using the parent key and a 32-bit index.
Normal vs. Hardened Derivation
Each level in the tree can produce 231 normal child keys (indices 0 to 231-1) and 231 hardened child keys (indices 231 to 232-1, denoted with ').
- Normal derivation — uses the parent public key + chain code. Allows deriving child public keys from an xpub without the private key.
- Hardened derivation — uses the parent private key + chain code. Prevents child key compromise from propagating upward to the parent.
Hardened derivation (indicated by an apostrophe, e.g.,
m/44') creates a cryptographic firewall between tree levels. If a child private key and its chain code are both leaked, hardened derivation prevents the attacker from computing the parent private key. This is critical for multi-account security isolation.
The Derivation Function
How do ECDSA and Schnorr signatures secure transactions?
ECDSA and Schnorr Signatures
Bitcoin historically uses the secp256k1 elliptic curve with ECDSA (Elliptic Curve Digital Signature Algorithm) for transaction signing. The Taproot upgrade (BIP340) introduced Schnorr signatures as an alternative.
ECDSA Signing Process
- Generate a random nonce
k(using RFC 6979 deterministic nonce generation) - Compute point
R = k × G(elliptic curve point multiplication) - Compute
r = R.x mod n - Compute
s = k-1(hash + r × privateKey) mod n - The signature is the pair
(r, s)
The fundamental security primitive is the Elliptic Curve Discrete Logarithm Problem (ECDLP) — given P = k × G, computing k from P and G is computationally infeasible.
Schnorr Signatures (BIP340)
Schnorr signatures offer several advantages over ECDSA:
- Linearity — signatures can be aggregated (key aggregation for multi-sig looks like a single signature on-chain)
- Provable security — security reduction directly to the discrete logarithm problem
- Smaller and faster — 64-byte signatures vs. variable-length DER-encoded ECDSA
- Batch verification — multiple signatures can be verified faster than individually
k in ECDSA immediately leaks the private key. RFC 6979 eliminates this risk by deriving k deterministically from the private key and message hash, ensuring the same input always produces the same (safe) nonce.
What are extended public keys (xpub) and watch-only wallets?
Extended Public Keys (xpub) and Watch-Only
An extended public key (xpub) encodes the public key together with its chain code, enabling the derivation of all normal child public keys without access to any private key. This enables powerful use cases:
- Watch-only wallets — monitor balances and generate receiving addresses without spending capability
- Payment servers — an e-commerce backend can generate a unique address for each customer using the xpub, while the private key stays offline on a hardware wallet
- Auditing — share your xpub with an accountant for tax reporting without granting spending access
- Multi-device setups — a phone watches balances while a hardware wallet handles signing
Version Prefixes
Different BIP standards use different version prefixes for extended keys:
| Public | Private | Standard | Address Type |
|---|---|---|---|
| xpub | xprv | BIP44 | Legacy P2PKH |
| ypub | yprv | BIP49 | Nested SegWit P2SH-P2WPKH |
| zpub | zprv | BIP84 | Native SegWit P2WPKH |
What is the difference between the UTXO model and account model?
UTXO Model vs. Account Model
How a wallet tracks and spends funds depends on the underlying blockchain model. The two dominant models are fundamentally different in design:
UTXO Model (Bitcoin, Litecoin, Cardano)
In the Unspent Transaction Output (UTXO) model, there is no concept of a "balance." Instead, your wallet scans the blockchain for unspent outputs assigned to your addresses. To spend, you consume one or more UTXOs as inputs and create new outputs:
- Each UTXO can only be spent once and in full
- If the UTXO exceeds the payment amount, the wallet creates a change output back to itself
- Transaction fees are implicit:
fee = sum(inputs) - sum(outputs)
Account Model (Ethereum, Solana, BNB Chain)
The account model works more like a traditional bank account — each address has a balance and a nonce (transaction counter). Transactions debit from one account and credit to another:
- Simpler mental model — just "balance minus amount"
- No change outputs needed
- Nonce prevents replay attacks (each transaction must have a unique, sequential nonce)
What are the different Bitcoin address types and script formats?
Address Types and Script Formats
Bitcoin supports multiple address types, each corresponding to a different script template that defines the spending conditions:
P2PKH (Pay-to-Public-Key-Hash)
The original Bitcoin address format. The locking script requires a signature and public key that hashes to the specified value. Addresses start with 1.
P2SH (Pay-to-Script-Hash)
Allows arbitrary spending conditions encoded in a script. The sender only needs the hash of the script — the full script is revealed at spending time. This enables multi-sig, time-locks, and other complex conditions. Addresses start with 3.
P2WPKH (Native SegWit)
Segregated Witness version 0. Moves signature data to a separate "witness" structure outside the base transaction, reducing the effective size and thus the fee. Addresses use Bech32 encoding and start with bc1q.
P2TR (Taproot)
The latest address type (SegWit v1), combining Schnorr signatures with MAST (Merkelized Abstract Syntax Trees). A P2TR output can be spent either via a key path (simple Schnorr signature) or a script path (reveals only the executed branch of a script tree). Addresses use Bech32m encoding and start with bc1p.
[ FREQUENTLY ASKED QUESTIONS ]
FAQ
[ READ NEXT ]
Continue Learning
Anatomy of a Seed Phrase
What makes up a BIP39 mnemonic, how entropy and checksums work, and why your 12-24 words matter.
The 25th Word (Passphrase)
How an optional BIP39 passphrase adds an extra security layer and enables hidden wallets.
Wallet Types Comparison
Hot wallets, cold wallets, hardware devices, multi-sig setups. Compare trade-offs and find the right fit.
Test Your Knowledge
Take a quick quiz to check your understanding of this guide.